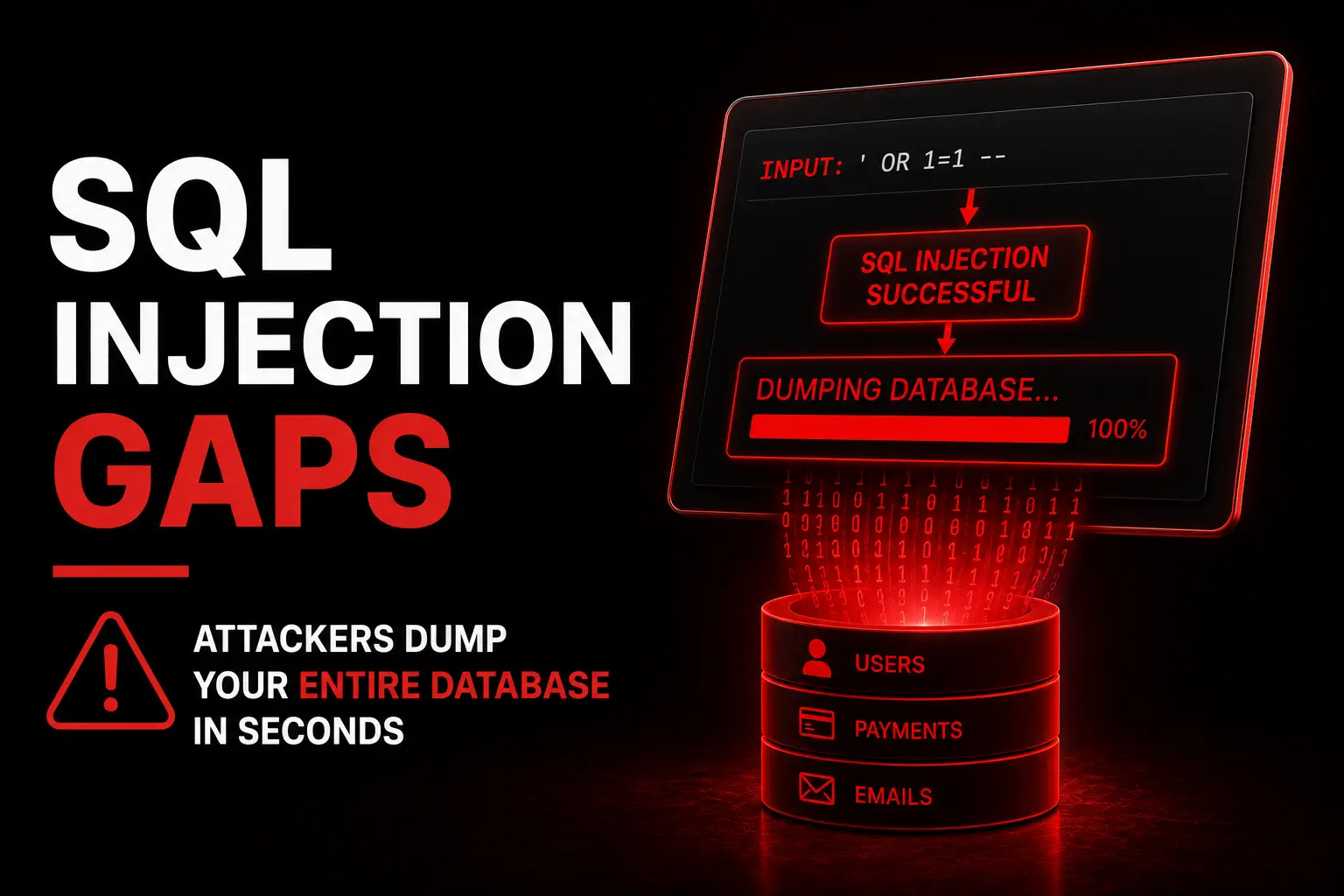
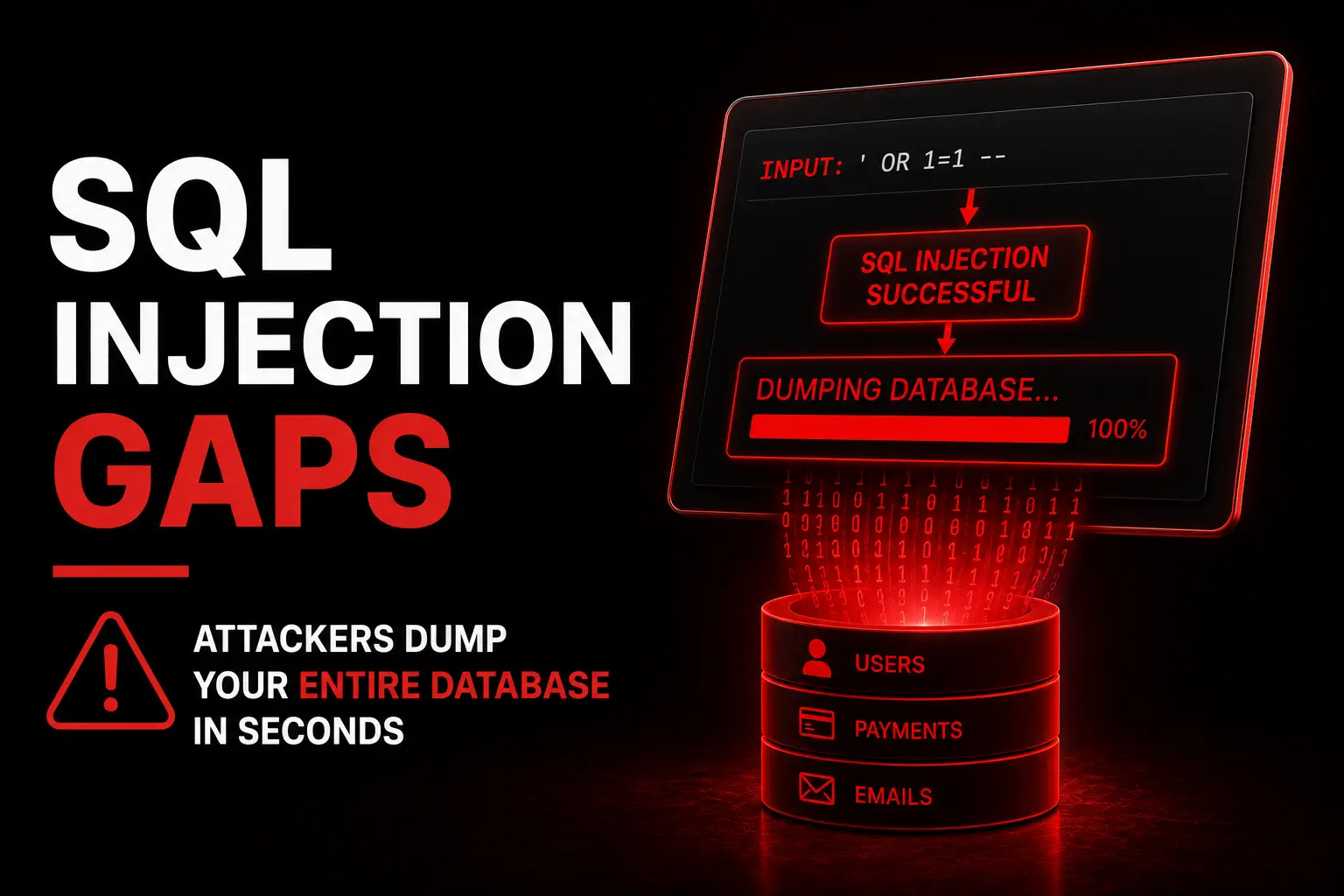
SQL Injection Gaps
Attackers dump your entire database in seconds. Unparameterised queries expose every customer record, password, and transaction to silent extraction.
A single breach wipes out years of trust overnight. We harden your website, applications, and data infrastructure so security becomes your competitive advantage — not your vulnerability.
Whether you know it or not, these vulnerabilities exist right now. Every one of them can be identified, patched, and monitored before an attacker finds them first.





43% of cyberattacks target small businesses. Most happen silently. Most are preventable.
Customers don't just want fast websites — they want safe ones. Every security gap is revenue leaking out. Every trust signal is a conversion multiplier.
We don't patch one hole — we harden every surface attackers could target
Attackers only need one gap. We find and close all of them — systematically, across every layer of your digital infrastructure.
Lock down your public-facing site — the first and most targeted attack surface your business has.
Secure every input, endpoint, and authentication flow in your app before attackers find them first.
Protect what matters most — customer data, business data, and your legal compliance status.
Harden the servers, networks, and cloud configuration that your entire business depends on.
Stop email spoofing, phishing, and credential theft — the #1 vector for successful attacks on SMBs.
Find every weakness before attackers do — with a detailed remediation roadmap ranked by severity.
This is a real-time view of what our WAF and monitoring stack blocks for protected clients. Unsecured sites face this alone.
A systematic process — not a one-off scan. Every gap found, prioritised, and permanently closed.
We scan every surface — code, server, email, config — with a 47-point checklist and produce a full severity-ranked report.
Three real clients. Three vulnerabilities that would have caused serious damage. All found and closed before attackers got there.
A UK fashion retailer's checkout API had a critical SQL injection vulnerability that had existed, undetected, for 11 months. Our audit found it on day two. The vulnerability would have exposed 34,000 customer records including payment tokens — triggering a GDPR breach notification, ICO fine, and catastrophic trust damage. We patched it, hardened the full API layer, and ran a post-fix pen test confirming clean status.
A SaaS accounting platform had no rate limiting on their login endpoint. Automated brute-force attacks were attempting 10,000 passwords per hour on admin accounts — completely invisible without monitoring. We implemented rate limiting, 2FA enforcement, anomaly-based login alerts, and deployed Cloudflare WAF rules. Within 72 hours of going live, the WAF blocked 43,000 attack attempts.
A law firm faced an ICO audit with significant GDPR gaps — no DPA register, missing consent mechanisms, weak data retention policies, and zero email authentication (making them trivially spoofable). We implemented GDPR compliance architecture, set up SPF/DKIM/DMARC, built a data processing register, and hardened staff access controls. They passed the ICO audit without a single corrective action.
One SQL injection breach costs an average of $4.45M. Our most comprehensive package costs a fraction of that — and prevents the breach entirely.
Full security audit + critical fixes — the minimum every website needs before going further.
Complete security hardening across all layers — website, app, data, email, infrastructure.
Enterprise-grade security for complex infrastructures, compliance requirements, and high-value targets.
Not sure which package you need? Book a free 20-minute security call — we'll tell you your biggest risk in the first 10 minutes.
The best security story is the one where nothing happens — because we got there first.
CheetahNova found a SQL injection in our checkout API that had been there for nearly a year. We had no idea. The thought of what that could have meant for our 34,000 customers — and our business — is terrifying. They fixed it in 48 hours.
Our login page was getting hammered with 10,000 brute-force attempts per hour and we didn't even know. The monitoring dashboard they set up showed us in real time. Within a week, everything was blocked. Game changer.
We had an ICO audit looming and knew our GDPR compliance wasn't where it needed to be. CheetahNova got us from 34% to 97% compliant in 3 weeks. We passed the audit with zero corrective actions — our legal team couldn't believe it.
They rebuilt our entire email authentication setup — we had none. Someone could have been sending emails as us to our clients and we'd have no idea. Now DMARC is at reject and we get weekly spoofing attempt reports. Incredible peace of mind.
The security score went from 29 to 94. I now show that report to enterprise prospects as a trust signal in our sales process. We've won three contracts specifically because security came up and we could prove our posture.
PCI DSS compliance felt like an impossible wall. CheetahNova broke it down into a phased plan, did most of the technical work for us, and got us compliant in time for our payment processor review. We didn't lose the deal.
Everything you need to know about our cybersecurity services.
CheetahNova cybersecurity services include website security reviews, web application security checks, vulnerability assessment, secure development support, technical security audits, protection planning and recommendations to reduce digital risk.
Yes. CheetahNova can review your website security, identify technical weaknesses, improve protection layers, check common vulnerabilities and recommend practical security improvements.
Yes. CheetahNova can support web application security by reviewing authentication flows, forms, APIs, admin panels, data handling, permissions and common web security risks.
Yes. A secure website or application helps protect customer data, reduce business risk and improve trust. Security also supports better reliability and a more professional digital experience.
Yes. CheetahNova can build or improve websites and applications with secure development practices, safer architecture, cleaner access control, protected forms, better validation and stronger technical foundations.
You can contact CheetahNova through the website, by email at info@cheetahnova.com or by phone at +44 7346 323799 to discuss your cybersecurity project.
Let's build your website with modern design, advanced SEO, and custom AI tools that automate your business and generate customers 24/7.
Free consultation • No commitment • Quick response